Code Release
This script is intended to assist in SCCM deployments of optional printers. The intended effect is to allow a user to open Software Center or the SCCM Application Catalog and click an option such as “Map me to XXX Printer”, and have the printer, port, and driver all install automatically.
Parameters
DriverName <Object> The name of the printer driver as defined in the INF file.
DriverInf <Object> Full path to the Driver INF file
DriverPath <Object> Path to the folder containing the driver files. (Default is the INF directory)
PrinterIP <Object> IP of the printer to map
PrinterPort <Object> Printer’s connection port. Default is 9100
PrinterPortName <Object> Name of the printer port. Defaults to “IP_<IP>”
PrinterCaption <Object> Name of the printer
Remove [<SwitchParameter>] Removes the specified printer instead of installing it
DriverOnly [<SwitchParameter>] Only installs the printer driver. Does not attempt to create the port or printer
AllSteps [<SwitchParameter>] Performs Driver install followed by the port and printer mappings. (Default without this and driver only is to only map a printer)
WriteLog [<SwitchParameter>] Writes Debug data to a log file. (Default is true)
RemoveAll [<SwitchParameter>] Removes all mapped printers. (You may need to run this once as the user, and once as an admin for full effect)
AdditionalRemovalExclusions <Object> When used with RemoveAll, prevents the removal of listed printers. By default, Send to One Note, and FAX are excluded.
Usage
PowerShell Script
To add a printer:
&"" -PrinterCaption "My Printer" -DriverName "Xerox 7845 PS v4" -PrinterIP "192.168.1.2"To add a driver:
&"" -DriverName "Xerox 7845 PS v4" -DriverInf "\\Drivers\Xerox\7845\Driver.inf" -DriverOnlyTo remove a printer and also disable logging
&"" Install-Printer.ps1 -PrinterCaption "My Printer" -Remove -WriteLog:$falseTo install a driver and then map a printer (Note that, in general, only administrators have the permissions to successfully use the script this way)
&"" -PrinterCaption "My Printer" -DriverName "Xerox 7845 PS v4" -DriverInf "\\Drivers\Xerox\7845\Driver.inf" -PrinterIP "192.168.1.2" -AllStepsTo remove all printers, or a selection of printers
&"" -RemoveAll -AdditionalRemovalExclusions @("My Printer", "Send by E-mail printer")SCCM Usage
To install a printer from SCCM, do the following.
- Create an application package for your driver. This can be an executable install or an INF install. If you are using an INF file, you may use the Install-Printer script to help.
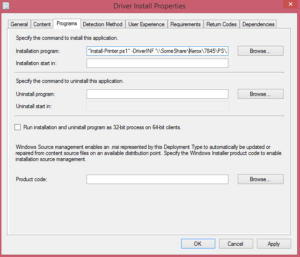
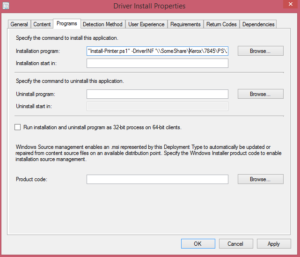
Example of the Driver Installation Programs Tab - To create an INF file Application deployment. Create a new application deployment. Set the command to
&"Install-Printer.ps1" -DriverOnly -DriverName '' -DriverINF ''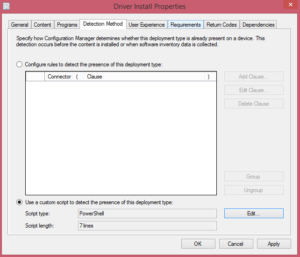
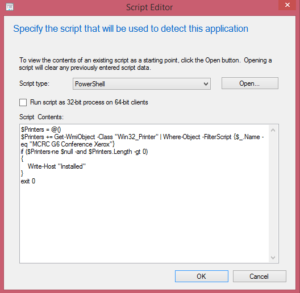
Example of the Driver Installation Detect Tab 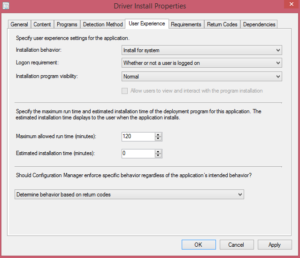
Example of the Driver User Experience Tab 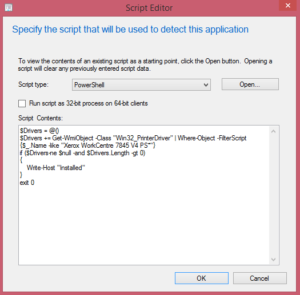
Example of the Driver Installation Detect Script - For the detection method, us the “Driver Detection” script in the “script” section of this page.
- To create an INF file Application deployment. Create a new application deployment. Set the command to
- Create an application package for your printer.
- Create a new Application Deployment. Set the command to “Install-Printer.ps1” -PrinterCaption ‘My Printer’ -DriverName ‘Xerox 7845 PS v4’ -PrinterIP ‘192.168.1.2’
Example of the Printer Installation Programs Tab - Set the detection method to the “Printer Detection” script in the “script” section of this page.
Example of the Printer Installation Detect Script - Set this package to install for the user.
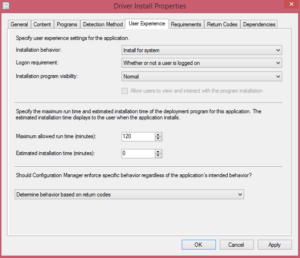
Example of the Printer Installation User Experience Tab - Add a requirement that points to the appropriate driver application package that you created earlier.
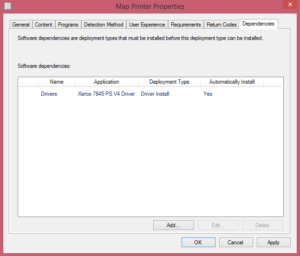
Example of the Printer Installation Dependency Tab
- Create a new Application Deployment. Set the command to “Install-Printer.ps1” -PrinterCaption ‘My Printer’ -DriverName ‘Xerox 7845 PS v4’ -PrinterIP ‘192.168.1.2’
Script
Install-Printer
<#
.SYNOPSIS
Provides helpfull script to add printers to a machine
.DESCRIPTION
Provides a method to add a printer, driver, and port to a machine
.PARAMETER DriverName
The name of the printer driver as defined in the INF file.
.PARAMETER DriverInf
Full path to the Driver INF file
.PARAMETER DriverPath
Path to the folder containing the driver files. (Default is the INF directory)
.PARAMETER PrinterIP
IP of the printer to map
.PARAMETER PrinterPort
Printer's connection port. Default is 9100
.PARAMETER PrinterPortName
Name of the printer port. Defaults to "IP_". If you need to map the printer to a default local port, use the name of the port instead. Such as "FILE:".
.PARAMETER PrinterCaption
Name of the printer
.PARAMETER Remove
Removes the specified printer instead of installing it
.PARAMETER DriverOnly
Only installs the printer driver. Does not attempt to create the port or printer
.PARAMETER AllSteps
Performs Driver install followed by the port and printer mappings. (Default without this and driver only is to only map a printer)
.PARAMETER WriteLog
Writes Debug data to a log file. (Default is true)
.PARAMETER RemoveAll
Removes all mapped printers. (You may need to run this once as the user, and once as an admin for full effect)
.PARAMETER LocalPrinter
Specified that the printer is local to the machine. This is needed if mapping a non-network device. (Such as the XPS printer)
.PARAMTER PrinterOnly
Only maps a printer, does not add a port, nor install a driver.
.PARAMETER AdditionalRemovalExclusions
When used with RemoveAll, prevents the removal of listed printers. By default, Send to One Note, and FAX are excluded.
.OUTPUTS
Log file located at C:\Temp\.log
.EXAMPLE
Install-Printer.ps1 -PrinterCaption "My Printer" -DriverName "Xerox 7845 PS v4" -PrinterIP "192.168.1.2"
.EXAMPLE
Install-Printer.ps1 -DriverName "Xerox 7845 PS v4" -DriverInf "\\Drivers\Xerox\7845\Driver.inf" -DriverOnly
.EXAMPLE
Install-Printer.ps1 -PrinterCaption "My Printer" -Remove -WriteLog:$false
.EXAMPLE
Install-Printer.ps1 -PrinterCaption "My Printer" -DriverName "Xerox 7845 PS v4" -DriverInf "\\Drivers\Xerox\7845\Driver.inf" -PrinterIP "192.168.1.2" -AllSteps
.EXAMPLE
Install-Printer.ps1 -RemoveAll -AdditionalRemovalExclusions @("My Printer", "Send by E-mail printer")
.EXAMPLE
Install-Printer.ps1 -PrinterCaption 'Microsoft XPS Document Writer' -PrinterPortName 'FILE:' -DriverName 'Microsoft XPS Document Writer v4' -PrinterOnly -LocalPrinter
.NOTES
Version: 1.3
Author: Matthew Thompson
Creation Date: 2015-12-16
Purpose/Change: PrinterOnly, and LocalPrinter Features, Printer Removal by IP, Bug fix in event no printers exist and script is run to install one.
This script was heavily influenced by Kris Powell. (http://www.adminarsenal.com/admin-arsenal-blog/how-to-add-printers-with-powershell)
#>
[CmdletBinding()]
Param
(
[string]$DriverName,
[string]$DriverInf,
[string]$DriverPath={if ($DriverINF -ne $null){(Split-Path $DriverInf)}},
[string]$PrinterIP,
[int]$PrinterPort=9100,
[string]$PrinterPortName=("IP_"+$PrinterIP),
[string]$PrinterCaption,
[Switch]$Remove,
[switch]$DriverOnly,
[switch]$AllSteps,
[switch]$WriteLog=$true,
[switch]$RemoveAll,
[string[]]$AdditionalRemovalExclusions=@(),
[switch]$LocalPrinter,
[switch]$PrinterOnly
)
#Setup the exclusions for RemoveAll
$Exclusions = @("Fax", "Send To OneNote 2013", "Send To OneNote 2010", "Microsoft XPS Document Writer", "Microsoft XPS Document Writer v4")
$Exclusions+=$AdditionalRemovalExclusions
$Log=""
#Log File Info
$ScriptName = Split-Path -Leaf $PSCommandPath
$LogFile = Join-Path -Path "C:\Windows\Temp" -ChildPath ($ScriptName+".log")
#Do a self-referential lookup to get the script version. As long as the .NOTES section of the file header is up to date and the script is trusted, this should work.
(Get-Help $PSCommandPath -Full -ErrorAction SilentlyContinue).alertset.alert.Text -match "^\s*Version\s*:\s*[\w\d\.\,]*" | Out-Null
if ($matches-ne$null-and$matches.Count-ge1)
{
$Version = $matches[0] -replace "^\s*Version\s*:\s*",""
}
#Write log data
$Log+="Version: "+$Version+"`r`n"
#Write Parameters to log
$PSBoundParameters.Keys | ForEach-Object -Process {$Log+=("`""+$_+"`" = `""+$PSBoundParameters[$_]+"`"`r`n")}
#Creates a printer object for the user.
function Create-Printer
{
Param
(
$PrinterCaption,
$PrinterPortName,
$DriverName,
[Switch]$Local=$false
)
try
{
$Printers = @()
$Printers += Get-WmiObject -Class "Win32_Printer"
[string]$Log="Installed Printers ("+$Printers.Length.ToString()+") `r`n"
$Printers | ForEach-Object -Process {$Log+=$_.Name+"`r`n"}
if ($Printers.Length -eq 0 -or ($Printers.Name).Contains($PrinterCaption) -eq $false)
{
$Log+="Attempting to create printer`r`n"
$Instance = Set-WmiInstance -Class "Win32_Printer" -Arguments @{Caption = $PrinterCaption;DriverName = $DriverName;PortName = $PrinterPortName;DeviceID = $PrinterCaption;Network = (-not $Local)} -ErrorAction Stop
if ($Instance -ne $null)
{
$Log+= "Printer Created`r`n"+$Instance.ToString()+"`r`n"
}
else
{
$Log+="Install attempted, but printer null`r`n"
}
}
$Log+= "Printer Exists: "+(($Printers.Name).Contains($PrinterCaption)).ToString()+"`r`n"
}
catch
{
$Log+=$_.ToString()+"`r`n"
}
return $Log
}
#Installs a driver from an INF file
function Install-Driver
{
Param
(
$DriverName,
$DriverPath,
$DriverInf
)
$Log=""
try
{
$Drivers = @()
$Drivers += Get-WmiObject -Class "Win32_PrinterDriver"
if ($Drivers.Length -eq 0 -or -not ($Drivers | Where-Object -FilterScript {$_.Name -like ($DriverName+"*")}))
{
$Instance = ([wmiclass]"Win32_PrinterDriver").CreateInstance()
$Instance.Name = $DriverName
$Instance.DriverPath = $DriverPath
$Instance.InfName = $DriverInf
Invoke-WmiMethod -Class "Win32_PrinterDriver" -Name "AddPrinterDriver" -ArgumentList @($Instance) -Impersonation Impersonate -EnableAllPrivileges | Out-Null
$Log+= $Instance.ToString()+"`r`n"
}
else
{
$Log+= ("Driver Exists: "+(($Drivers | Where-Object -FilterScript {$_.Name -like ($DriverName+"*")})).ToString())+"`r`n"
}
}
catch
{
$Log+=$_.ToString()+"`r`n"
}
return $Log
}
#Creates a printer port required to map a printer
function Create-PrinterPort
{
Param
(
$PrinterIP,
$PrinterPort,
$PrinterPortName
)
$Log=""
try
{
$PrinterPorts = @()
$PrinterPorts += Get-WmiObject -Class "Win32_TCPIPPrinterPort"
if ($PrinterPorts.Length -eq 0 -or -not ($PrinterPorts.Name).Contains($PrinterPortName))
{
$Instance = Set-WmiInstance -Class "Win32_TCPIPPrinterPort" -Arguments @{Name = $PrinterPortName;HostAddress = $PrinterIP;PortNumber = $PrinterPort;SNMPEnabled = $false;Protocol = 1}
$Log+= $Instance.ToString()+"`r`n"
}
else
{
$Log+= ("Printer Port Exists: "+(($PrinterPorts.Name).Contains($PrinterPortName)).ToString())+"`r`n"
}
}
catch
{
$Log+=$_.ToString()+"`r`n"
}
return $Log
}
function Get-PrinterPort
{
Param($IP)
$Log=""
$ToReturn = @()
try
{
$PrinterPorts = @()
$PrinterPorts += Get-WmiObject -Class "Win32_TCPIPPrinterPort"
if ($PrinterPorts.Length -eq 0 -or -not ($PrinterPorts.HostAddress).Contains($IP))
{
#$Instance = Set-WmiInstance -Class "Win32_TCPIPPrinterPort" -Arguments @{Name = $PrinterPortName;HostAddress = $PrinterIP;PortNumber = $PrinterPort;SNMPEnabled = $false;Protocol = 1}
$Log+= "No Printer Port exists matching $IP"
}
else
{
$ToReturn = $PrinterPorts | Where-Object -FilterScript {$_.HostAddress -eq $IP}
$Log+= ("Printer Port Exists: "+(($PrinterPorts.Name).Contains($PrinterPortName)).ToString())+"`r`n"
}
}
catch
{
$Log+=$_.ToString()+"`r`n"
}
return $ToReturn
}
#Deletes an already mapped printer
function Delete-Printer
{
Param($PrinterName, $IP)
$Log=""
try
{
$Printers = @()
$Printers += Get-WmiObject -Class "Win32_Printer"
if ($PrinterName -ne $null)
{
$Printers = $Printers | Where-Object -FilterScript {$_.Name -eq $PrinterName}
}
elseif ($IP -ne $null)
{
$Ports = Get-PrinterPort -IP $IP
$NewPrinterList = @()
foreach ($Port in $Ports)
{
$NewPrinterList += $Printers | Where-Object -FilterScript {$_.PortName -eq $Port.Name}
}
$Printers = $NewPrinterList
}
else
{
$Log+="No parameters specified to limit removal. No printers removed"
return $Log
}
foreach($Printer in $Printers)
{
$Printer.Delete() | Out-Null
$Log+= $Printer.Name+" deleted`r`n"
}
}
catch
{
$Log+=$_.ToString()+"`r`n"
}
return $Log
}
#Script Entry
if ($Remove)
{
Write-Host "Removing $PrinterCaption"
#Remove a printer selected
$Log+=Delete-Printer -PrinterName $PrinterCaption -IP $PrinterIP
}
elseif($RemoveAll)
{
#Remove most printers
$Printers = @()
$Printers += Get-WmiObject -Class "Win32_Printer" | Where-Object -FilterScript {$Exclusions.Contains($_.Name) -eq $false}
if ($Printers.Length -gt 0)
{
Write-Host ("Attempting to remove "+$Printers.Length+" printers. You may need to run this script once as admin, and once as the user for all printers to be removed.")
foreach($Printer in $Printers)
{
$Log+=(Delete-Printer -PrinterName $Printer.Name)+"`r`n"
}
}
else
{
Write-Host "No printers require removal."
}
}
else
{
#Install a printer
if ($DriverOnly -or $AllSteps)
{
#Install the printer Driver
Write-Host "Installing $DriverName"
$Log+=(Install-Driver -DriverName $DriverName -DriverPath $DriverPath -DriverInf $DriverInf)+"`r`n"
}
if (-not $DriverOnly -and -not $PrinterOnly)
{
#Output for user visibility
Write-Host "Mapping printer ($PrinterCaption) from IP $PrinterIP"
#Add the printer port
$Log+=(Create-PrinterPort -PrinterIP $PrinterIP -PrinterPort $PrinterPort -PrinterPortName $PrinterPortName)+"`r`n"
#Finally, create the printer
$Log+=(Create-Printer -PrinterCaption $PrinterCaption -PrinterPortName $PrinterPortName -DriverName $DriverName -Local $LocalPrinter)+"`r`n"
}
if ($PrinterOnly)
{
#Output for user visibility
Write-Host "Mapping printer ($PrinterCaption) from port $PrinterPortName"
$Log+=(Create-Printer -PrinterCaption $PrinterCaption -PrinterPortName $PrinterPortName -DriverName $DriverName -Local $LocalPrinter)+"`r`n"
}
}
#Write the log to a file
if ($WriteLog)
{
$Log | Out-file $LogFile
Write-Verbose $Log
}Driver Detection
Edit the “lt;DriverName>” Portion of the script below with the name of your driver. Then add the script into SCCM as your script-based detection method for the INF driver installation.
#Note that this script is not perfect, you may need to change the detection method if you have multiple similiarly named drivers.
$DriverName = "" #Replace this with your driver name
$Drivers = Get-WmiObject -Class "Win32_PrinterDriver"
if (($Drivers | Where-Object -FilterScript {$_.Name -like ($DriverName+"*")}))
{
Write-Host "Driver already installed"
}
exit 0Printer Detection
Edit the “<PrinterName>” portion of the script below with your own printer name. Then add this to your printer deployment as the script-based detection method.
$PrinterCaption = "" #Change this to your printer name
$Printers = Get-WmiObject -Class "Win32_Printer"
if (($Printers.Name).Contains($PrinterCaption))
{
Write-Host "Printer already installed"
}
exit 0Remove-Printer (Interactive Printer Removal Tool)
This must be placed in the same directory as Install-Printer.ps1 This will present a user with a list of printers to exclude. The user can then select a printer by inputting it’s number. If they do, it will be excluded. Once finished, the script will remove all other printers.
<# .SYNOPSIS Interactively assists a user in removing printers .DESCRIPTION Interactively assists a user in removing printers .NOTES Version: 1.0 Author: Matthew Thompson Creation Date: 2017-01-08 Purpose/Change: Updated for Blog #>
#Printers to exclude by default
$Exclusions = @("Fax", "Send To OneNote 2013", "Send To OneNote 2010")
#Grab a list of printers
$Printers = Get-WmiObject -Class "Win32_Printer" | Where-Object -FilterScript {$Exclusions.Contains($_.Name) -eq $false}
#Stores additional exclusions by user
$AdditionalExclusions=@()
#Infinite loop (Breaks out with user interaction)
while($true)
{
Write-Host "Printers to remove:"
#Print all non excluded printers for user to browse
$NonExcluded=@()
$NonExcluded += $Printers | Where-Object -FilterScript {$AdditionalExclusions.Contains($_.Name) -eq $false}
for($I=0;$I -lt $NonExcluded.Length;$I++)
{
Write-Host ($I.ToString()+") "+$NonExcluded[$I].Name)
}
#Ask user to exlude another printer or continue
$UInput = Read-Host -Prompt "Please select a printer to exclude or type `"f`" to finish"
if ($UInput.ToLower() -eq "f")
{
#On continue, break out of infinite loop
break;
}
#Otherwise matching selected index to printer, and add.
$UIndex=$null
if ([int]::TryParse($UInput, [ref]$UIndex) -and $UIndex -ge 0 -and $UIndex -lt $NonExcluded.Length)
{
$AdditionalExclusions+=$NonExcluded[$UIndex].Name
}
else
{
#In case someone can't type a number
Write-Host "Input could not be parsed, please try again"
}
}
#Call the parent script with the selected exclusions
Write-Host "Removing printers"
&".\Install-Printer.ps1" -RemoveAll -AdditionalRemovalExclusions $AdditionalExclusions -WriteLog